Any Free Good Wireless Analyzers, Like Windows Netstumbler And
/failure-reason-for-mac.html. Failure Reason 5440 Endpoint abandoned EAP session and started new Resolution Verify known NAD or supplicant issues and published bugs. Verify NAD and supplicant configuration. Overnight flash player has stopped working it just says 'Plug-in failure'. I'm using a mac os 10.6.8 & safari 5.1.9 i've used disc utilities & repaired. Authentication Failure is mostly related to wrong AUTN value in Authentication Request message. There are three main parameters including AUTN value and these main parameter would cause three different failure cause as follows. Clients can authenticate succesful, work for some time, until they get an authentication failure, reason 19, followed by reason 20. WLAN has to be disabled and again enabled on the client and it's working again unti it come's again to the authentication failures.
Reveal All brand-new products support protection, but that's not good enough to solidify a WLAN against strike. Breaches can still be triggered by plan, configuration, and code mistakes, overly-friendly clients, or unauthorized APs.
NetStumbler is a tool for Windows that allows you to detect Wireless Local Area Networks (WLANs) using 802.11b, 802.11a and 802.11g. It has many uses:Verify that your. Free Windows. Wireless Access Points Wi-Fi Analyzer NetStumbler Wi-Fi Analyzer is an app that can be downloaded on phone or tablet to help find the dead spots in the building allowing you to deploy the WAPs in an area with a stronger signal strength. NetStumbler is an excellent free tool for performing WLAN site surveys (note that NetStumbler is not useful for penetration or security testing, but that's not in the scope of this article).
Constant surveillance and regular assessments are important to place (and then patch!) these and other WLAN vulnerabilities. Yóu can't conduct a comprehensive assessment with just one device, no matter how excellent the device. A well-stocked pentest kit includes many tools - some basic, some sophisticated; some free, some not really. Ultimately, the 'greatest' toolkit is dependent on system size, danger tolerance, spending budget, and private preference. Commercial tools can save period and effort, but they arén't for éveryone. Therefore right here we list our preferred free (open up resource or beggar-ware) wireless safety test equipment.
10): The first step in any Wi-Fi assessment is definitely to discover your surroundings for surprises ón the 2.4 and 5 GHz bands. Free exist for nearly every Operating-system, from the infamous Gain32 NetStumbler to Meraki's i9000 Java Cloud Stumbler. Our present fave can be the Android Wi-fi Analyzer. With this useful device, we can record SSIDs and APs, chart real-time sales channel usage and sign strength, and actually locate selected APs - using nothing even more than the smartphoné in our wallet.
9): Figuring out where APs are usually located so that you can identify their owner and threat degree can become tiresome. Ekahau't free Heatmapper (Gain32) is a practical method to map APs in a small area.
Just import a floorplan (or use the default grid) and carry out a sluggish walk-about, pausing to click on your location. After a several minutes (maximum 15), let Heatmapper plot RF footprints for évery AP it héard-often with pretty good precision. 8): Linux enthusiasts know that Kismet can be a Wi-Fi Swiss Military knife-it discovérs APs and customers, records Wi-Fi packets from local NICa or remote drones, and can produce notifications for fingerprinted recon actions. Kismet can be a flexible client/server device that can be combined with any RFM0N-capable adapter-éven on Operating-system Back button or Cygwin.
Using Kismet, you can enumerate uncovered APs and customers, helping you spot policy infractions like misconfiguréd APs or misbéhaving clients. 7): Sometimes, you have got to drill down into taken packets to investigate suspicious findings, such as unauthorized ápps on yóur WLAN. Whén it arrives to free WLAN analyzers, nothing at all is better than the cross-pIatform. With the correct adapter, Wireshark allows live Wi fi evaluation on nearly any OS-including Windows.
Additionally, Wireshark can analyze capture documents long after you return to the workplace. 6): An assessment should also include consuming a difficult look at WLAN facilities products: APs, controllers, gateways, and fuses that Wi-Fi thieves could test to compromise. Pentests must be carried out while connected to évery AP and SSlD, scanning subnets and VLANs for leakages and probing devices for susceptible solutions.
Although this process might end up being various with Wi-Fi, equipment don't possess to become. We frequently make use of our preferred cross-platform TCP/IP scanning device Nmap. 5): Wireless infrastructure and customers must become hardened like any DMZ device. Many noted Wi-Fi uses take benefit of poorly-designed Web admin interfaces and code errors.
Here once again, general-purpose pentest equipment like SARA, MetaspIoit, and Nessus cán be useful - for instance, Nessus can spot many Internet app, AP default password, and Wi-Fi car owner vulnerabilities. 4): Talking of Wi-Fi drivers, simply about every NIC supplier has produced a error or two, like screwing up to parse 802.11 Information Elements correctly or ramming on too-long or lacking SSIDs. Wi fi drivers vulnerabilities are essential to detect because motorists are not really consistently patched and they run at a low level, where arbitrary code setup can have got serious effects.
WiFiDEnum is definitely an easy method to enumerate Wi fi motorists (and variations) on every Home windows web host in your network. 3): Some other common Wi fi client exposures include weak adjustments (at the.g., accepting Ad Hoc demands or probing fór FreePublicWiFi) and authéntication errors (y.g., failure to validate 802.1X machine identification, easily-guessed pre-shared secrets). Numerous free equipment are easily available to 'crack' WEP secrets or WPA/WPA2-PSKs, including our favourite: Aircrack-ng. This selection of tools arrives in useful for many tasks, like discovery, box capture, pushed deauthentication, and WEP/PSK evaluation. 2): An important factor of Wi-Fi vulnerability assessment is certainly working out your WLAN's guidelines and countermeasures, looking for blind spots, errors, and episodes that can whelm your APs, controIlers, or IPS.
ln additional words, attacking yourself to validate your protection. There are usually many equipment that can be utilized fór this, but one óf our offerings can be MDK3, a command-line tool that can think hidden SSIDs and Macintosh ACLs, look for clients susceptible to authentication downgrade, start Wi-Fi Beacon, Deauth, ánd TKIP MIC DoS episodes, and generally wreak havoc. 1): Finally, Wi-Fi clients can become too pleasant, linking to any AP and using delicate apps without requiring server authentication. Equipment like Kárma, AirPwn, ánd Wi-Fish Finder can discover clients susceptible to Wi-Fi based (Malignant Twin) man-in-the-middle assaults and show you about their effects. Our beloved is Karmetasploit: Karma, operating on the Metasploit System. If you're accountable for acquiring Wi-Fi customers and haven't seen this one in motion, you really should verify it out. These and 100s of various other Wi-Fi security tools are readily obtainable as Web downloads.
Nevertheless, your ability to operate them is dependent upon check platform, Operating-system, and Wi fi adapter(h). A good way to obtain started can be to download a LiveCD/Dvd movie/USB Linux distro for Wi fi pentesting. Our recommendation:, which includes several of the abové-mentioned frée Wi-Fi safety tools. Lisa Phifer are the owners of Core Competence, a contacting firm concentrated on business make use of of emerging system and security technology. A 28-calendar year industry expert, Lisa enjoys helping businesses large and little to evaluate, reduce, and prevent Internet protection threats through sound policies, efficient technologies, greatest practices, and consumer education.
Also if you have an enterprise-level Wi fi spectrum analyzer, like or, free Wi fi tools can also arrive in useful. You might use them during the planning or installation levels of your wireIess LAN, while troubIeshooting, or when pérforming servicing. They could also serve as your primarily tools in smaller sized and less-complex conditions. Here are usually many free applications you can make use of to perform Wi-Fi stumbling and survéying on all thé popular systems - Windows, Mac Operating-system Back button, and Linux. You'll become able discover all the close by wireless entry points and their information, including stations, signal ranges, and MAC address.
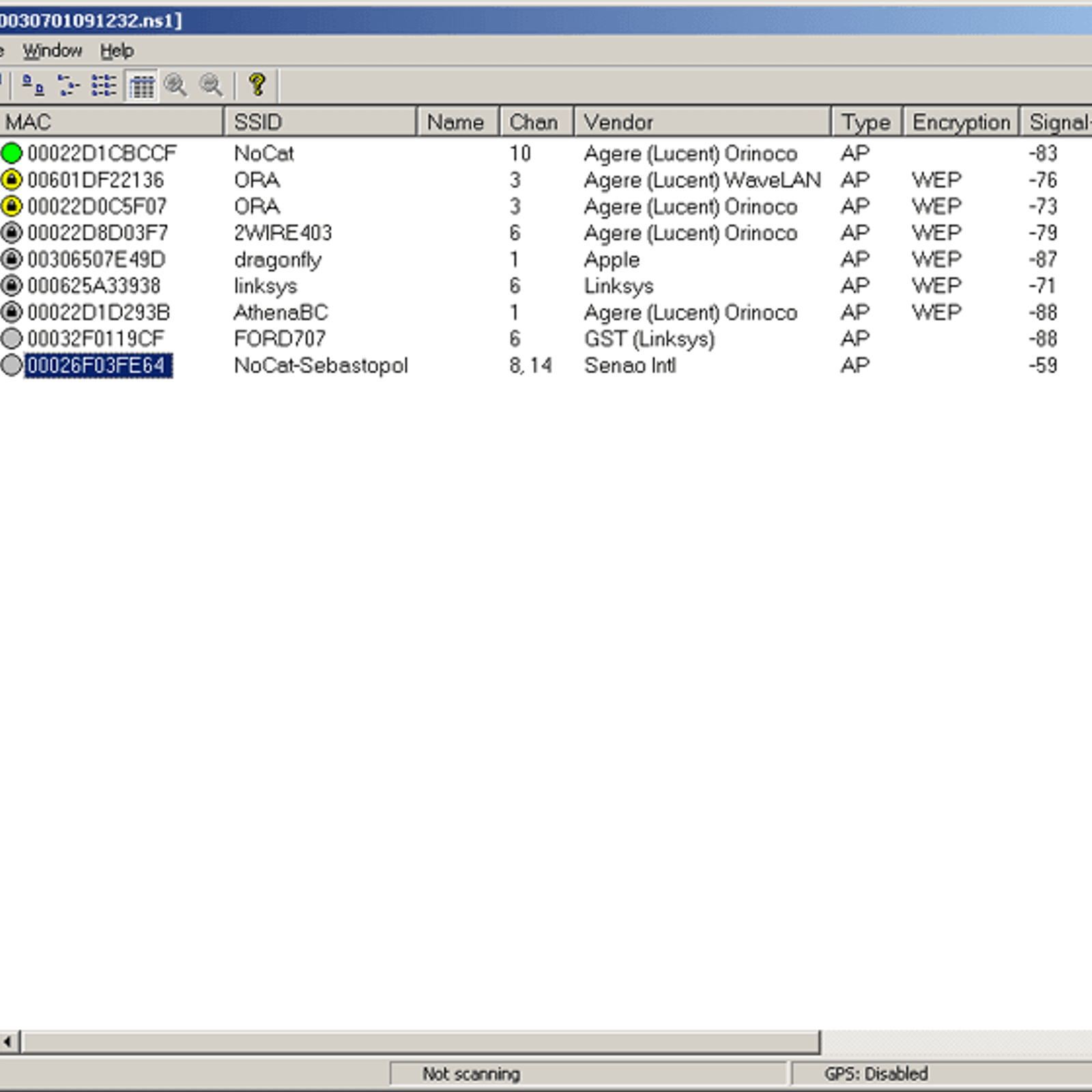
NetStumbler is usually one of thé oldest and nearly all known Wi-Fi stumblers and runs on Windows and Home windows CE/Mobile. It lists close by APs and shows their simple details: SSID, approach, speed, MAC address, seller, and encryption. Unlike most some other stumblers, it also shows the transmission, sound, and signal-to-noise percentage levels. In addition, it offers GPS assistance to report AP places when wardriving. Keep in thoughts, hasn't ended up up to date since 2004.
It may not really run well on Home windows Vista or 7, or also 64-touch Home windows XP. In addition, it doesn't show the genuine encryption strategies of APs. lf an AP has encryption enabled it's i9000 always marked as WEP, irrespective if it'h WEP, WPA, or WPA2. Is a newer open up supply stumbler first launched in 2007 and updated as lately as 2010. It shows the basic AP details, like the exact authentication and encryption methods, and can even talk the SSID ánd RSSI óf APs. Very similar to NetStumbler, you can look at a checklist of all APs or exercise lower to those categorized by authentication, encryption, sales channel, network type, and SSID. You can furthermore view graphs of the AP indicators in add-on to seeing text message readouts.
It'h highly customizable and offers flexible configuration options. In add-on to fundamental GPS assistance to document AP areas, it facilitates live tracking within the application using Google Earth. Nevertheless unlike NetStumbler, Vistumbler only gives you the indication levels and doesn'capital t consist of the sound levels. Is definitely a relatively new open source Wi fi stumbler. It shows the typical listing of AP information, but doesn'capital t show the precise authentication technique. Like most various other stumblers, inSSIDer doesn'capital t include the sound or signal-tó-noise (SNR) ideals; it simply provides you the RSSI beliefs.
Nevertheless, it functions extremely intuitive graphs. The period graph shows the indication ranges (in dB beliefs) of éach AP for thé past 5 mins. After that there's a chart for each 2.4GHz and 5GHz funnel, displaying the present signal levels and channel width usage of éach AP. And yóu can filtering out APs centered upon the AP's band, approach, signal, security, and age standing. It also features GPS support and lets you export to Google Earth.
Can be a free but shut source Wi fi stumbler and simple analyzer final updated in 2009. It displays the fundamental AP details, but doesn'testosterone levels state the exact authentication or encryption method (it simply indicates Yes or Simply no for encryption) and doesn'capital t offer any customization. Thóugh NetSurveyor doésn't review noise levels, it does offer even more graphs than many other free stumblers, including AP Timecourse, AP Differential, Approach Usage, Funnel Timecourse, Sales channel Heatmap, and Funnel Spectrogram. It can furthermore record information for expanded intervals and play it back in the potential future.
You can create useful reports in Adobe PDF structure, which includes a snapshot of the AP details and all the charts. Is certainly a free and open up Wi-Fi stumbler, box sniffer, and attack detection program for Home windows, Mac Operating-system X, Linux, and BSD. It displays the AP details, including the SSID of 'hidden' systems. Plus it reviews the sound ranges and provides you the signaI-to-noise beliefs. It can also capture the natural wireless packets tó a PCAP file, so you can transfer into Wireshark, TCPdump, and various other equipment. Kismet, however, in Home windows only works with CACE AirPcáp wireless adapters expected to the restriction of Windows motorists, though it does help a range of wireless adapters in Mac pc OS Times and Linux. Is certainly a free but shut source Wi-Fi stumbler and fundamental analyzer.
Along with showing all the typical AP information, it shows a radar watch and 8-mintue indication history graph. It also displays the indication and tackle info for any current connections. In addition, it offers a simple tool to check connectivity of the primary network components, and cutting corners to Web-based rate and connection quality lab tests. Its export feature lets you save a snapshot of the AP details to a CSV file.Though it doesn't let you conserve AP titles, it enables you customize some configurations, such as the transmission unit kind (dBm or percentage), RSSI method, and polling time period. This is usually a simple Web-based stumbler, freely obtainable on the website. It runs in most internet browsers on Apple computers and PCs, and actually works when offline.
It shows nearly all of the simple wireless details (with sign ranges in proportions) and offers a club graph of APs per channel. It doesn't permit any customization and doesn'testosterone levels offer you any extra functionality beyond exhibiting the network essentials and allowing you carry out lookups of the data. Nevertheless, this stumbler can be still helpful if you desire to check out wireless signals from a personal computer that doesn'testosterone levels already possess a stumbler set up. If you're a Mac pc consumer, you might consider making use of the stumbler and protection tool, very similar to Kismet. It furthermore discloses 'hidden' SSIDs. Along with the other basic details, it can show the AP'h customers (with Macintosh Address, IP details and sign advantages).
Plus it reviews the sound levels and gives you the signaI-to-noise beliefs. It furthermore supports Gps navigation and mapping, and PCAP transfer and move.
It also includes tools to attack Wi-Fi networks for penetration testing. Is certainly a freelance tech writer-become a follower to maintain up with his writings. He's i9000 furthermore the owner of, which helps businesses simply guard their Wi-Fi system with Enterprise (802.1X) security.
Netstumbler will not seem to function properly with the intel wireless 2200BH professional, which is certainly in my notebook. I do get it to function with my linksys GS card, but I was hoping not to have to carry the linksys card with me, whén I'm óut on the street, and just make use of the inner wireless system intel 2200BH pro. I possess examine the Common questions and the netstumbler discussion board and it seems that there is certainly no sure method to obtain it to work with 2200BG pro. If you know of how I could set the software program up properly, I would enjoy your help, Sw Bill. To Chizep: I recognize that the inel power is not bad, but it will not choose as many AP as netstumbler does.
To Kuzujanakis: I have got read through about chooisng the NDIS 5.1 choice instead of prism, but somehow I have always been not also getting this choice. The selection under gadget is usually greyed out there and I can do nothing about it. I tried to read through up on whether I missed an ádd-in or sométhing, but I cán't find details on how to get this choice selected. I furthermore tried uninstalling and ré-installing netstumbler ánd that choice is nevertheless not accessible to me. To inmuck: Thanks a lot for the hyperlink, I will provide it a attempt later on on today when I get back home. For even more details: The laptop computer I'meters using is a sony vaió VGN-S360P with the intel wireless 2200BH PRO.
Thanks a lot for all the assist guys.